$285M Drift Protocol Hack: A Turning Point for Crypto Security

A $285M exploit on the Solana-based Drift Protocol reveals a shift in crypto threat models as attackers target humans, not code.
On April 1, 2026, the Drift Protocol, a prominent Solana-based decentralized finance (DeFi) platform, suffered a devastating exploit resulting in the theft of $285 million. What set this attack apart was not a vulnerability in the platform’s code but a meticulously executed social engineering campaign targeting the humans behind the protocol. This incident highlights a paradigm shift in cybersecurity for decentralized platforms, emphasizing that the weakest link is often not the code but the people managing it.
The Scale of the Breach
Drift Protocol was once a pivotal part of the Solana DeFi ecosystem, enabling users to trade derivatives and capitalize on lucrative yield vaults. Before the breach, it had $550 million in total value locked and had passed stringent audits by respected firms such as Trail of Bits and Claw Secure. Yet, on that ill-fated April morning, Drift’s official channels confirmed the exploit, dispelling any notion that it was merely an April Fool’s prank.
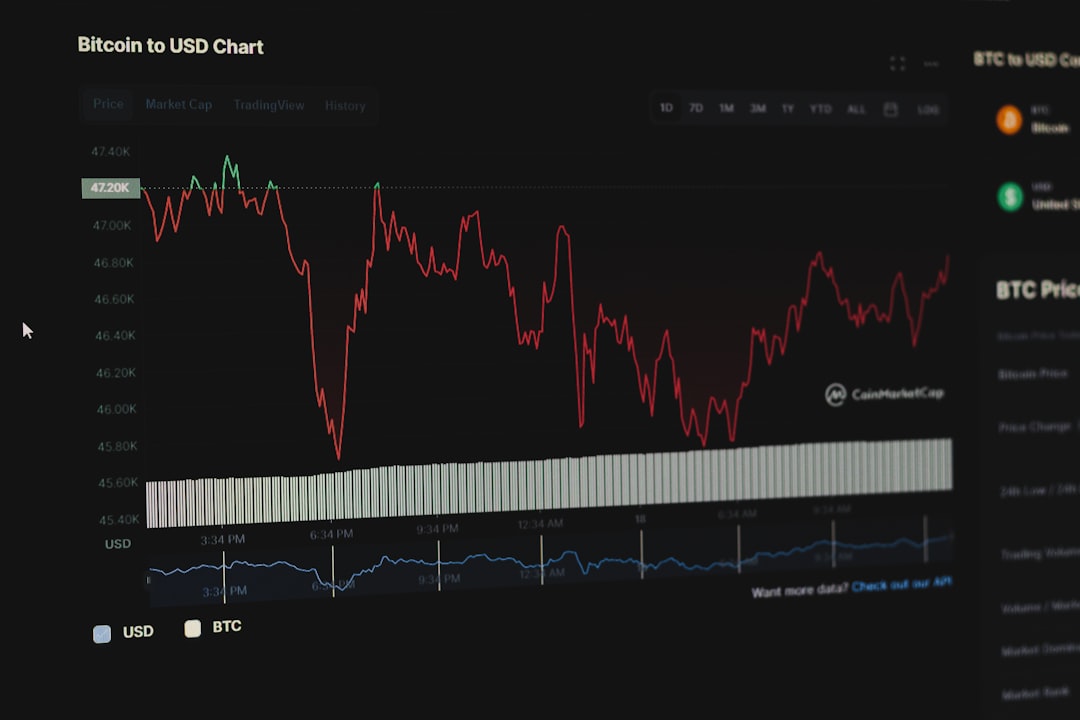
The impact was immediate and catastrophic. Drift’s native token lost 97% of its value from its 52-week high, as a panic-induced selloff unfolded. The ripple effect extended well beyond Drift, affecting up to 20 interconnected protocols reliant on its liquidity, marking the incident as the largest DeFi exploit in Solana’s history.
The Human-Centric Strategy
Unlike prior attacks exploiting flaws in smart contracts or cryptographic mechanisms, this operation was an exercise in exploiting trust. Analysts have attributed the attack to North Korean state-affiliated actors, specifically a group identified as UNC4736. Remarkably, the breach began six months earlier, around autumn 2025, at a major international crypto conference.
At the conference, Drift contributors were approached by individuals posing as representatives of a legitimate and successful quantitative trading firm. These agents, likely intermediaries, possessed exceptional technical knowledge, making it easy to pass due diligence checks. Over the following months, these actors built trust by creating a Telegram group with Drift’s core contributors, attending multiple conferences, and even funding an ecosystem vault with $1 million of their own capital. This calculated approach allowed them to gradually gain insider status within the protocol.
The Technical Intrusion
The operational phase of the attack involved two key compromises. First, the attackers disseminated a GitHub repository that reportedly contained a standard front-end integration for the vault they funded. In reality, the repository exploited a vulnerability in the Visual Studio Code (VS Code) development environment. A subtle but lethal configuration file manipulated the environment’s auto-run tasks feature, enabling the attackers to compromise developers’ systems silently.
Second, they convinced a Drift contributor to download a fraudulent test application, further compromising devices. These two vectors provided the attackers with the ability to monitor the signing infrastructure used by Drift’s Security Council without triggering suspicion.
Exploiting Governance Mechanisms
The final stage of the attack exploited Solana’s durable nonces, a feature that permits transactions to be signed offline and executed later. Between March 23 and March 30, the attackers convinced Security Council members to presign seemingly routine administrative transactions. These transactions, however, contained hidden authorizations to transfer full control of the protocol to the attackers.
Compounding the issue, Drift disabled its administrative time lock during a routine Security Council migration, eliminating the system’s last safety barrier. By the time the durable nonce transactions were broadcast on April 1, the attackers faced no safeguards against immediate execution.
The Heist
The actual theft unfolded rapidly. At 9:30 a.m. Pyongyang local time on March 12, the attackers began preliminary preparations, such as withdrawing 10 ETH from the Tornado Cash mixer to fund operations. On April 1, they deployed a fabricated token, Carbon Vote, and manipulated its price through wash trading to create the illusion of substantial value.
With administrative control secured, the attackers listed the inflated Carbon Vote token as valid collateral, tricking the protocol’s risk engine into recognizing $750 million in phantom assets. Within 12 minutes, they drained $155 million in Jupiter liquidity provider tokens, SOL, wrapped BTC, and other tokens from nearly 20 pools. These were converted into stablecoins via decentralized exchanges and bridged to Ethereum, where they were dispersed across thousands of wallets. Notably, blockchain investigators criticized Circle, the stablecoin issuer, for missing the opportunity to freeze the illicit transfers during the seven-hour bridging process.
Attribution and Consequences
Security firms like Elliptic have attributed the attack with medium to high confidence to UNC4736, which previously orchestrated similar exploits, including the $50 million Radiant Capital hack in 2024. The Drift Protocol exploit reflects an escalation in both scale and sophistication, signaling that state-sponsored entities are evolving their capabilities to fund sanctioned regimes through systemic financial theft.
Post-attack, the probability of asset recovery is deemed nearly zero. The exploit underscores a stark reality: human trust, not code, has become the primary vulnerability in decentralized systems.
A Crisis for DeFi Security
The Drift exploit reshapes the threat landscape for DeFi. The attack’s success shows that even the most rigorously audited protocols are vulnerable unless every layer of operation, from governance design to individual human interactions, is secured.
Security experts are urging protocols to reconsider governance structures. A key recommendation is the implementation of mandatory time locks for administrative transactions to prevent unilateral and instantaneous takeovers. Enhancing the security of development environments and limiting the exposure of signing infrastructure are also crucial steps.
However, the broader implication is sobering: as DeFi matures, it becomes a more attractive target for state-level actors. This means the crypto industry must anticipate not just opportunistic hacks but also sophisticated, well-funded campaigns aimed at exploiting every conceivable vulnerability, including human relationships.
While smart contract audits and technical security measures remain essential, they are insufficient on their own. Protocols must address the human element, whether through robust operational procedures, zero-trust frameworks, or stronger safeguards. The Drift Protocol hack serves as a wake-up call that trust itself can be weaponized, and protecting it must be a central tenet of the DeFi ecosystem moving forward.
Staff Writer
Priya writes about blockchain technology, DeFi, and digital currency regulation.
Comments
Loading comments…